クラウドワークロード保護プラットフォーム
緊急性の高い脆弱性を優先付けし、コンテナへの脅威を数秒で検知
従来のセキュリティツールでは、コンテナ化されたワークロードの可視化ができないうえ、延々とアラートが生成されてしまいます。クラウドの保護には、脆弱性を優先付けし、脅威を即座に検知できることが不可欠です。
Sysdigが提供する価値とは?
コンテナのセキュリティには、クラウドのコンテキストが不可欠
コンテナセキュリティを次のレベルに引き上げます。クラウド全体にわたる調査結果を活用してワークロード保護を強化し、最も重大なリスクを優先付けします。コンテナとKubernetes全体にわたる脅威と脆弱性の完全な可視性とコンテキストを得ましょう。
-
最もリスクの高い組み合わせを特定する
コンテナへの脅威を個別に見るだけでは不十分です。コンテナとクラウド間のマルチドメイン相関分析により、リスク中心の視点でワークロードのセキュリティにアプローチし、最も重要なリスクを優先付けします。隠れた攻撃経路を明らかにし、攻撃者を足止めします。
-
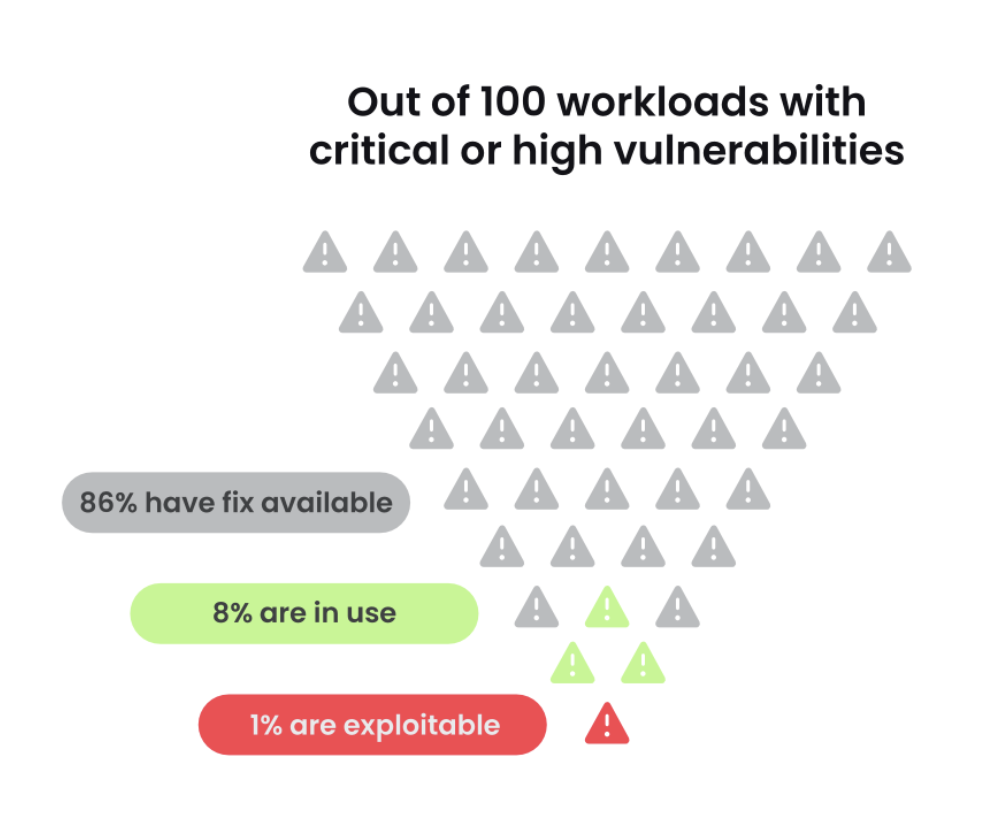
時間を短縮し、脆弱性ノイズを削減
エージェントベースとエージェントレスの脆弱性スキャンを併用することで、双方のメリットを最大限に活用できます。ランタイム・インサイトを使用して、使用中のパッケージに関連する脆弱性を優先付けし、脆弱性ノイズの95%をフィルタリングします。エージェントレスのアプローチを使用してセットアップとスキャンを簡素化し、クラウド環境全体で脆弱性を検出します。
-
数秒でワークロード上の脅威を検知
クラウド上での攻撃の実行にかかる時間ははわずか10分。Sysdigを併用すれば、コンテナ、Kubernetes、サーバー全体で脅威をリアルタイムで検知できます。対話型コマンド、システムコール、監査ログなどの関連コンテキストをキャプチャして、数分で脅威を調査し、対応します。
無料ガイド
Kubernetes保護のベストプラクティス
Kubernetesは開発者によるマイクロサービスへの移行を促進しますが、同時に複雑なセキュリティ上の課題をもたらし、その課題がデプロイ段階まで対応されないままになります。クラウドネイティブなセキュリティへの積極的なアプローチを確実にするためのベストプラクティスを入手しましょう。
数値による証明
CWPPがどのように役立っているか?よくある質問とその回答
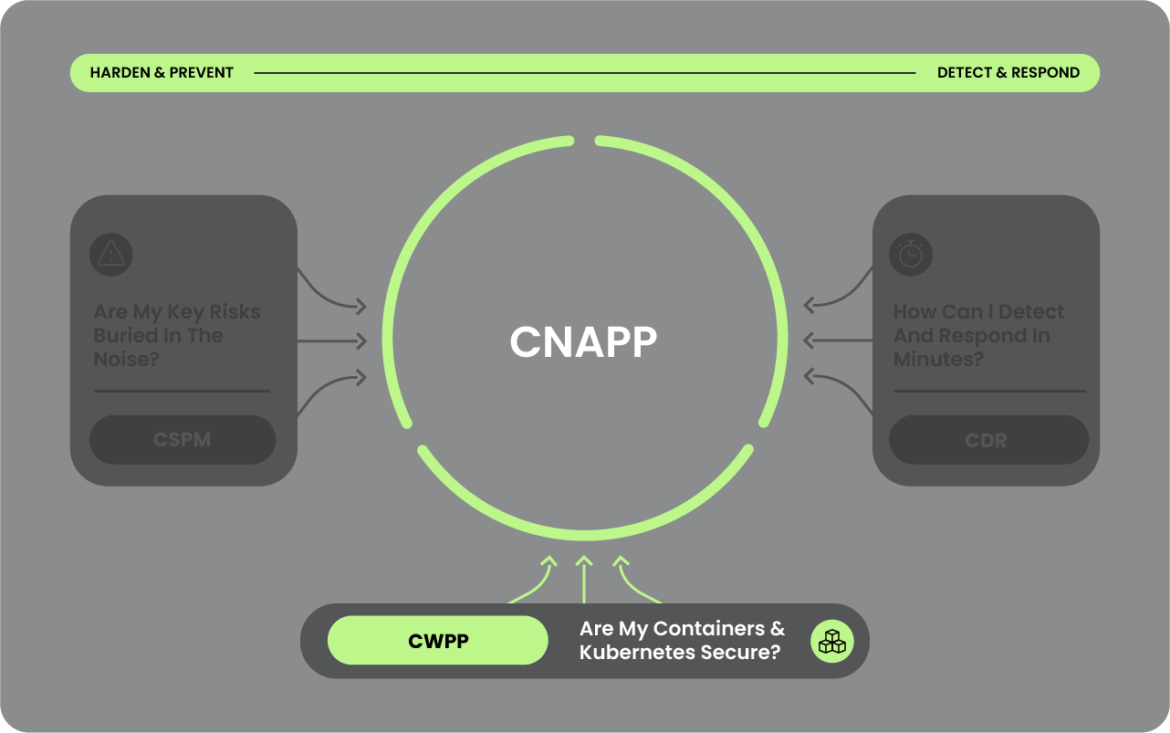
クラウドワークロード保護プラットフォーム(CWPP)は、物理サーバー、仮想マシン、コンテナ、サーバーレス機能を横断するクラウドベースのワークロードの保護に重点を置いたクラウドセキュリティソリューションです。 CWPPは主にクラウド上で実行されているものに焦点を当て、それらのワークロードを脅威から保護します。 CWPPが支援できることの例としては、脆弱性管理、検知と対応、コンテナ、Kubernetes、サーバーの実行時可視化などがあります。
従来の CSPM ソリューションは、セキュリティ対策における弱点を補強することで、クラウドインフラへの攻撃を防止することに重点を置いています。CWPP ソリューションは、そのインフラ上で実行されるワークロードの防御と検知の両方を組み込んでいます。
CSPMとCWPPは、クラウドネイティブなアプリケーション保護プラットフォーム(CNAPP)に統合すべきであり、そうすることで複数の異なるソリューションが不要になります。これらの機能を単一のプラットフォームに統合することで、インフラセキュリティとワークロード保護のギャップを埋めることができます。理想的なCNAPPソリューションは、ワークロードとより広範なクラウド環境全体で、調査結果とコンテキストの相関関係を提供すべきと考えています。
その他の参考資料
お問い合わせ
Sysdigでは個別デモの実演依頼を受け付けております。安心安全なクラウドネイティブ環境の実現方法にお悩みなら、ぜひお気軽にご相談ください。